WSR: #18: April 18th - 24th 2022
Active Directory hacking, Taking notes in Obsidian, and Windows Privilege Escalation
Published: April 24, 2022
| Reading Time: 3 minutes
This Week’s Recap
4/18/2022
- Read this amazing blog post on A blueprint for evading industry leading endpoint protection in 2022 and took notes in obsidian.
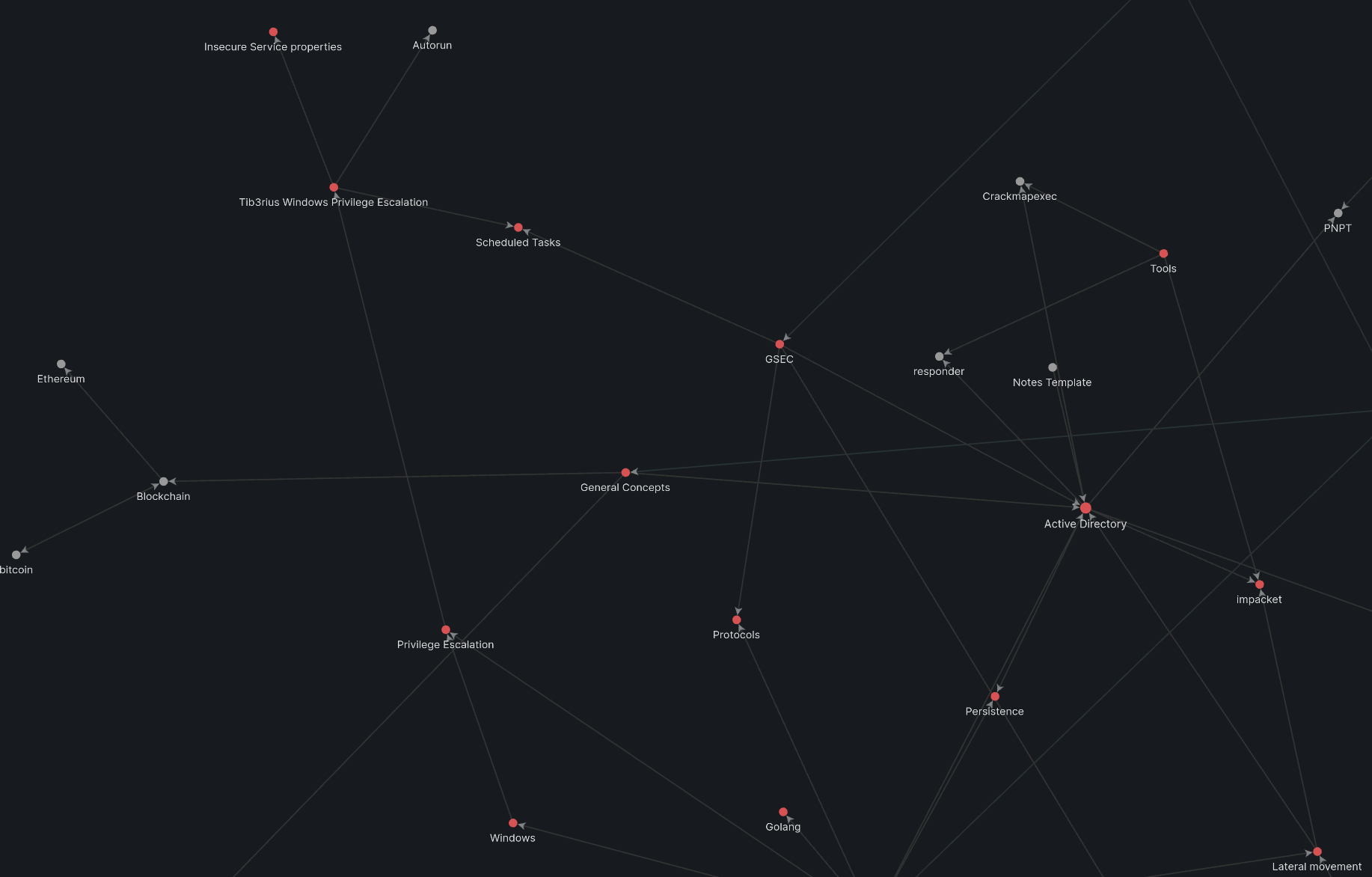
- I am working on a new note taking method in obsidian that will better allow me to link different notes together
- Started saving articles to pocket instead of just throwing into a random file
- Finished the Active Directory portion of the PNPT.
- Luckily most of this is a review from other certs/experience I have.
4/19/2022
- Started the windows privilege escalation portion of the PNPT.
- Admittedly , I am not great with anything windows. I have some experience writing powershell scripts to automate patching, software installation, etc but when it comes to actually hacking windows, I lack a lot of the practical skills you need for a real environment.
- Bought Tib3rius’s windows and Linux privilege escalation course on Udemy
4/20/2022
- Finished half of Tib3rius’s windows privilege escalation course, really great stuff. I enjoy this quick and to the point style of teaching.
- I also set up some VMs in my lab to work on my windows privilege escalation techniques.
- Continued to struggle with trying to figure out if I want to learn Go or C next. I’m leaning more towards C because I know C is going to be a lot more involved but I don’t think its something I’m going to regret learning. It also seems to be a solid entry point into other more red team-y type topics (EDR Evasion, reverse engineering, etc)
- Worked on my Wildwest Hackin’ Fest talk
4/21/2022
- Spent most of the day going through the rest of Tib3rius’s windows privilege escalation course and taking notes.
- Spent a lot of time fooling around in my lab running WinPeas, seatbelt, bloodhound, etc
- Found this great resource for Active Directory hacking called WADComs. It’s basically GTFO bins but for AD.
- Read through this cobalt strike article how how
getsystem works in metasploit. Pretty cool to learn what’s going on in the background.
- Worked on my Wildwest Hackin’ Fest talk
4/22/2022
4/23/2022
- Worked on my Wildwest Hackin’ Fest talk
- Did a lot of whats on the horizon planning.
- The next few weeks for me include WWHF, PNPT exam, starting GSTRT for my masters program, and buying the CRTO material. It’s going to be a busy summer…
4/24/2022
Have any questions
Do you have any questions? Feel free to reach out to me on twitter. See you next Sunday. :)