WSR: #17: April 10th - 17th 2022
Active Directory pentesting, PNPT, and chatting with David Alves
Published: April 17, 2022
| Reading Time: 3 minutes
This Week’s Recap
4/11/2022
- Decided to finally take the plunge and formally learn Active Directory. I know a lot about it already but my knowledge is very sporadic. Created an Active Directory lab on my proxmox instance (Which you can read about here) and ordered this active directory book.
- I’m also looking to get the PNPT soon so having an AD lab will knock out two birds with one stone.
4/12/2022
- Decided I needed to rethink my future planning system (at least for security stuff.)
- Currently I just have a mental list of “things I want to learn” but I needed something more formally laid out so I created an obsidian wiki to keep track of these different categories of stuff to learn.
- Side note, I’m actually using obsidian the way it is meant to be used (files linked together instead of tons of folders) so the graph feature actually works
4/13/2022
- Got access to the PNPT material to fill in the AD gaps I have. So far the course material has been fantastic, especially for the price. I will probably not go through the whole thing since a lot of it will be review but I cannot believe some of this is not taught in more expensive courses I’ve taken
4/14/2022
- Skipped to the AD portion of the PNPT material. A lot of it is review but its very nice to have a single place to learn from rather than jumping around to random youtube videos or blogs.
- Worked through this for a few hours and took notes in obsidian. Next step is to create an AD lab this weekend.
4/15/2022
- Got my bloodhound challenge coin from @_wald0!
- Worked through most of the AD portion of PNPT

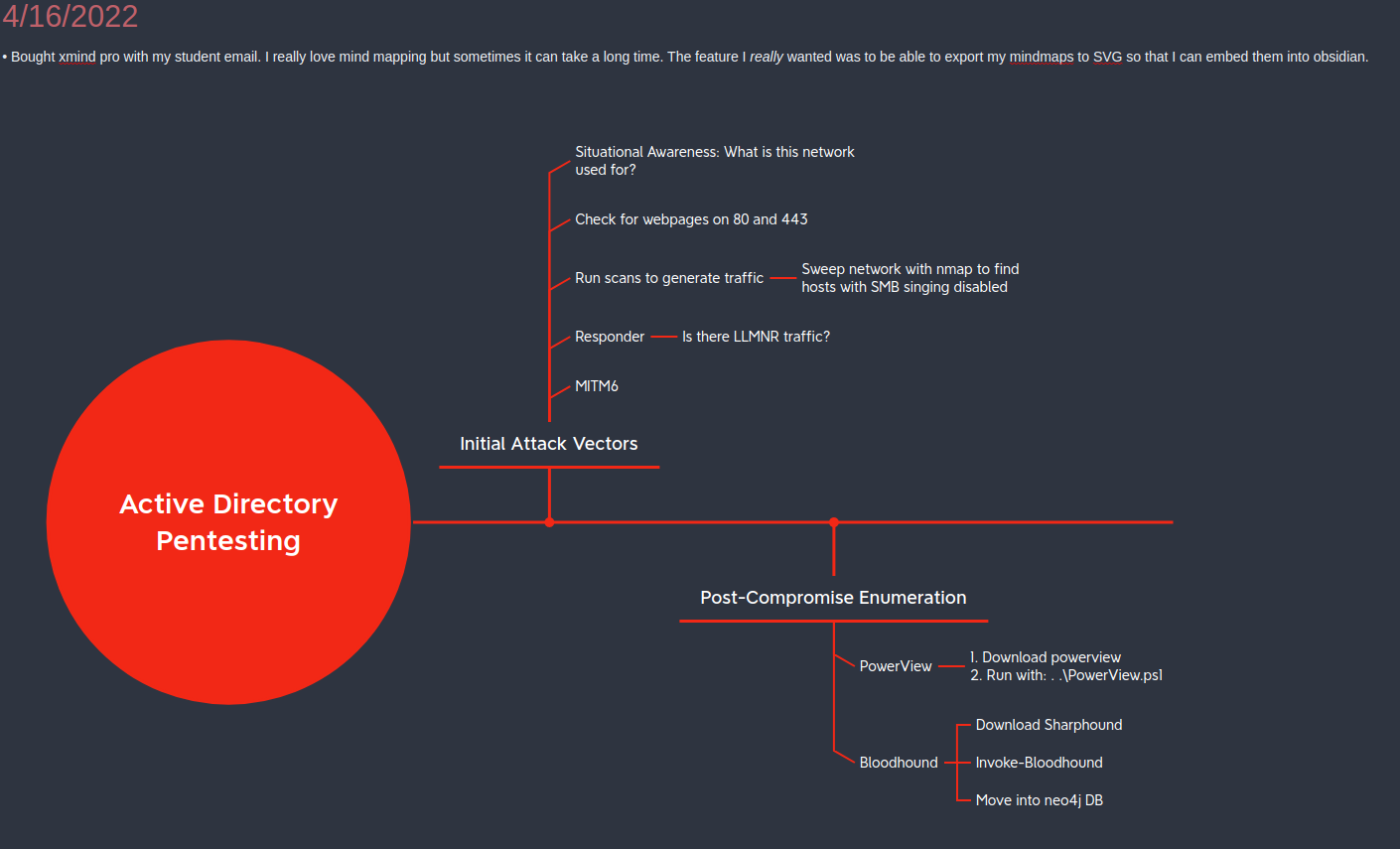
4/16/2022
- Bought xmind pro with my student discount. I really love mind mapping but sometimes it can take a long time. The feature I really wanted was to be able to export my mindmaps to SVG so that I can embed them into obsidian like so:
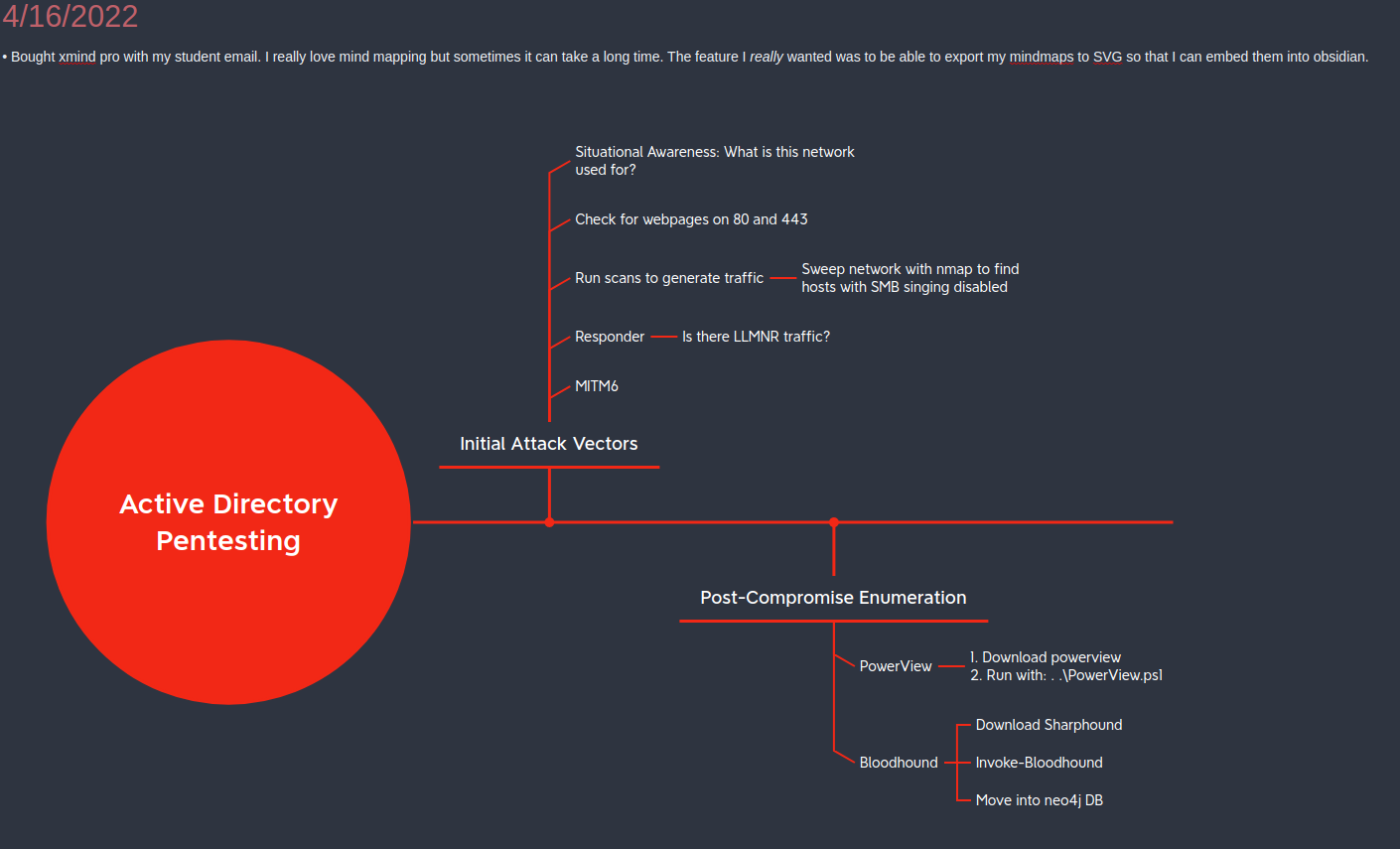
- Spent the rest of the day creating an AD lab. A lot of toubleshooting my proxmox instances but ended up getting a DC and two domain machines set up
- David Alves uploaded the first episode of his podcast. Super honored to be the first guest! Watch it here!

4/17/2022
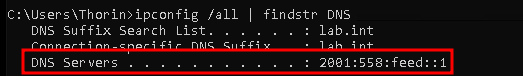
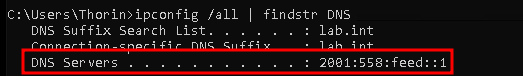
- Got very confused as to why my AD lab was using IPv6 for DNS but eventually fixed it by just disabling IPv6. This is obviously a temporary workout around because some of the fun attacks I want to do exploit IPv6 (such as mitm6)
Have any questions
Do you have any questions? Feel free to reach out to me on twitter. See you next Sunday. :)