WSR: #1: December 12-19th 2021
The first roundup!
Published: December 19, 2021
| Reading Time: 3 minutes
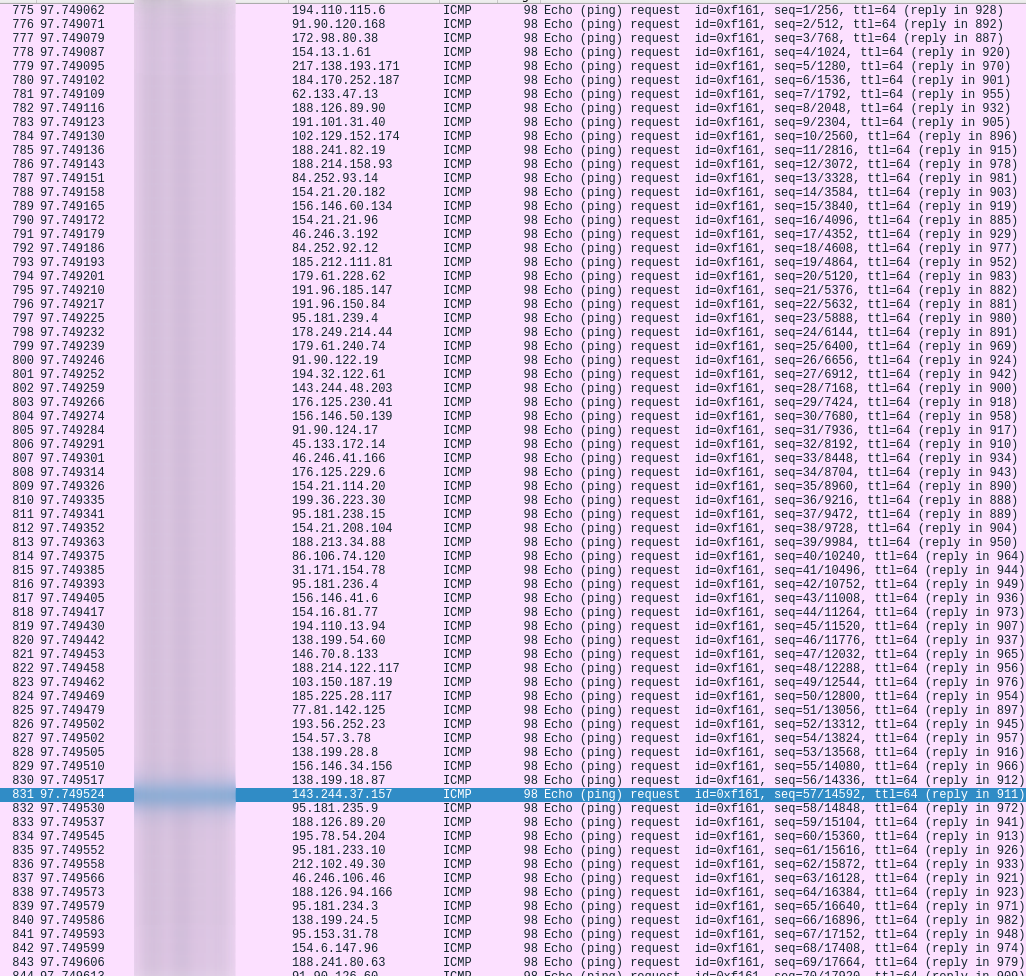
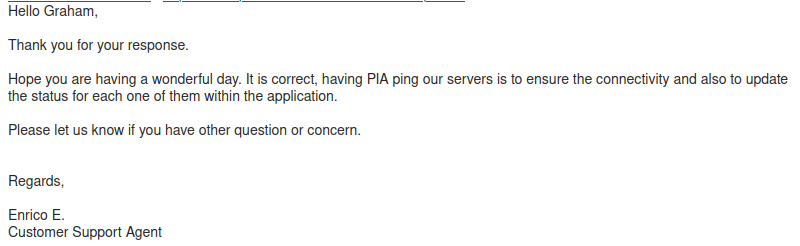
This is the first of a weekly “round up” that aims to summarize the security or IT related concepts I have worked on this week during my free time. My goal is to create a footprint for others to follow in if they so desire. When I was first learning the basics of security I struggled to find projects that I could work on to help me learn useful security practices and techniques. Some weeks will have have more content than others depending on the amount of free time I have. Discovered Unsupervised Learning by Daniel Miessler Watched A Tale of Two Johns (John hammond and John strand interview) Set up rsyslog server in my home lab via this tutorial (This was very easy) Investigated further with wireshark and found out it was an IGMP query packet to refresh the IPs of multicast group memberships. This was sent out by my router. Do you have any questions? Feel free to reach out to me on twitter. See you next Sunday. :)What is this?
12/12/2021

1# Docker learning resources
2https://www.youtube.com/watch?v=wCTTHhehJbU
3
4https://www.youtube.com/watch?v=3c-iBn73dDE&feature=youtu.be
5
6https://www.youtube.com/watch?v=MnUtHSpcdLQ&feature=youtu.be
12/13/2021
12/14/2021
12/15/2021

1sudo tcpdump -i <interface> -s 65535 -w sketchy.pcap
12/16/2021
12/17/2021
12/18/2021
12/19/2021
Have any questions